容器镜像安全扫描
最后更新时间:2024-12-02 14:49:53
操作场景
腾讯云容器镜像服务(Tencent Container Registry,TCR)企业版支持对托管的容器镜像进行安全扫描,生成扫描报告,暴露容器镜像内潜在的安全漏洞,并提供修复建议。容器镜像安全是云原生应用交付安全的重要一环,对上传的容器镜像进行及时安全扫描,并基于扫描结果选择阻断应用部署,可有效降低生产环境漏洞风险。
镜像安全扫描功能内置在镜像仓库中,用户可在上传容器镜像后,主动触发对指定版本容器镜像的安全扫描,也可以在命名空间层级配置自动扫描,该命名空间内新推送镜像上传完成后将自动被扫描。当前镜像安全扫描服务基于开源 Clair 方案,相关漏洞信息来自官方 CVE 漏洞库,并定期保持同步。
前提条件
在使用镜像安全扫描功能前,您需要完成以下准备工作:
已成功 购买企业版实例。
如果使用子账号进行操作,请参考 企业版授权方案示例 提前为子账号授予对应实例的操作权限。
操作步骤
配置扫描策略
1. 登录 容器镜像服务 控制台,选择左侧导航栏中的命名空间。
2. 在“命名空间”页面中,单击需开通镜像安全扫描功能的实例名称,进入命名空间详情页。
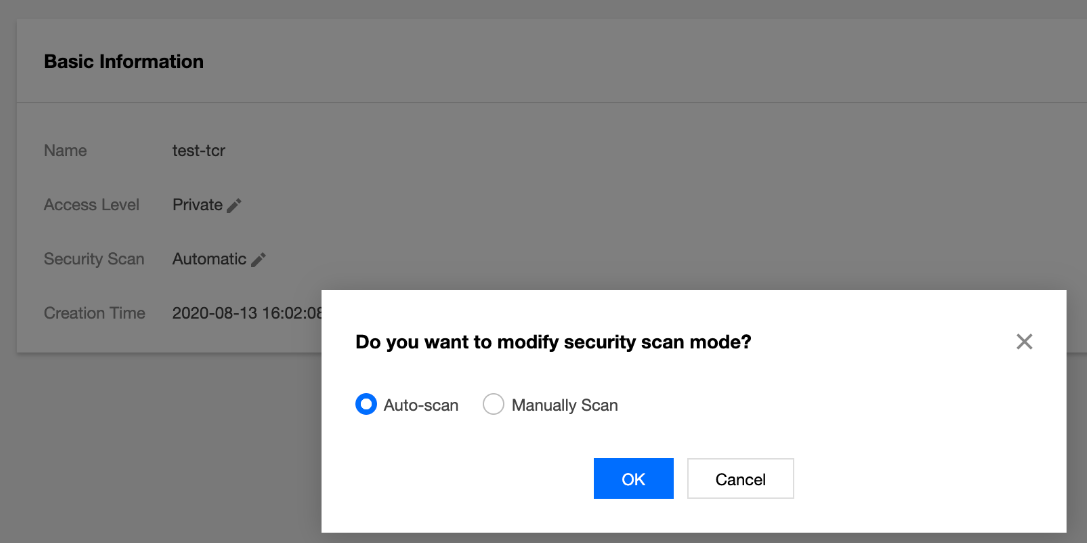
3. 在“基本信息”页,将安全扫描配置为自动扫描。如下图所示:
手动触发扫描
步骤1:准备容器镜像
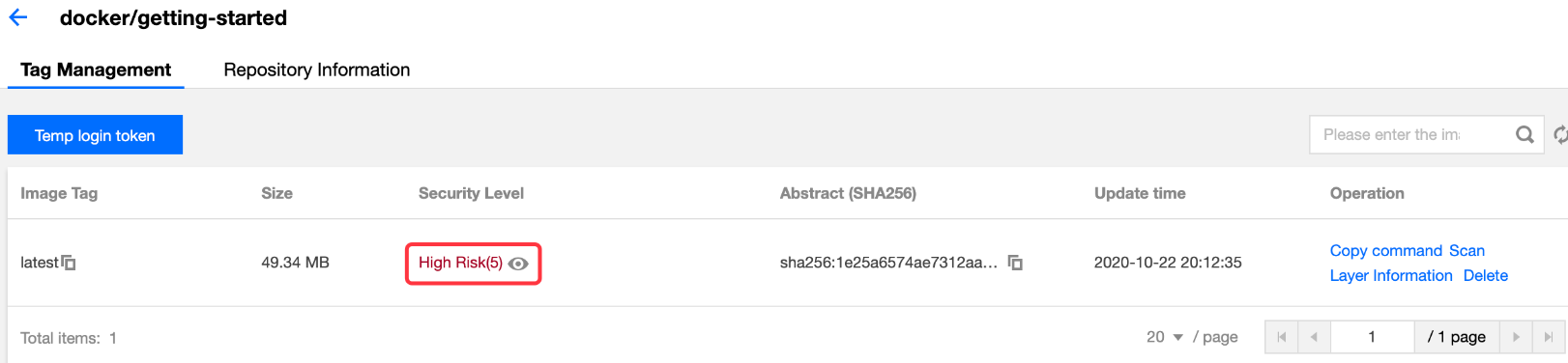
步骤2:触发镜像扫描
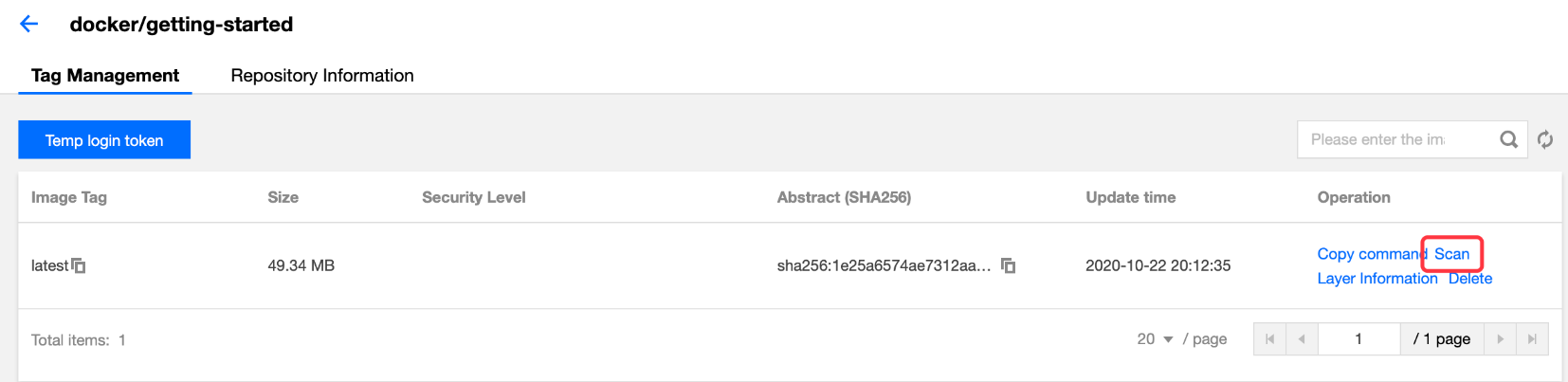
选择该镜像仓库内指定镜像版本,单击扫描触发镜像扫描,此时安全级别显示为“扫描中”。如下图所示:
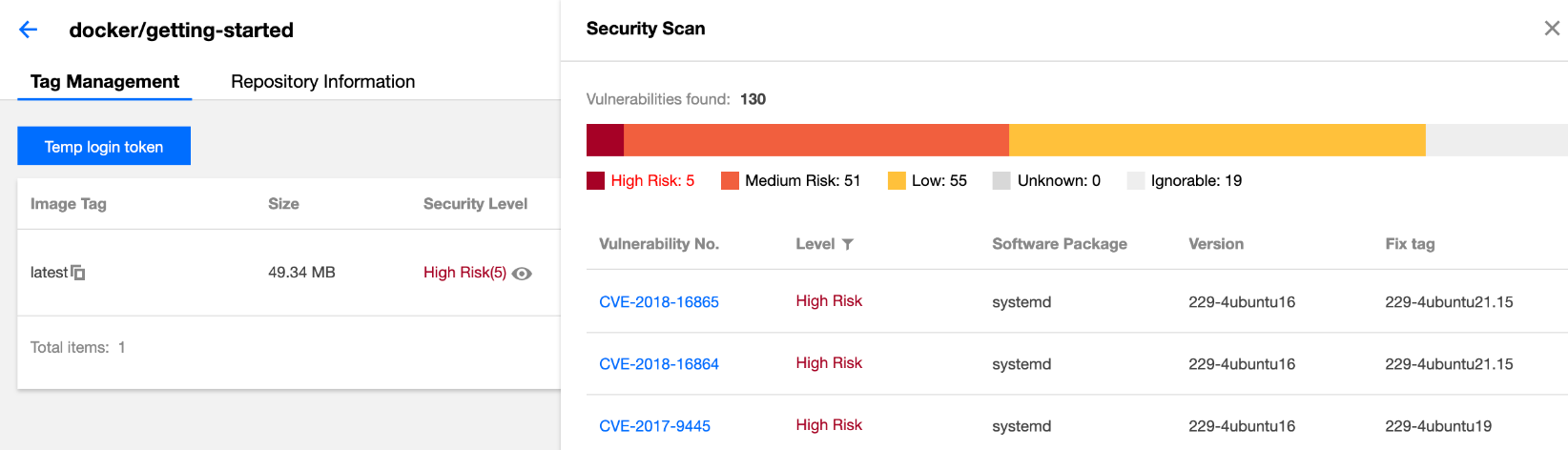
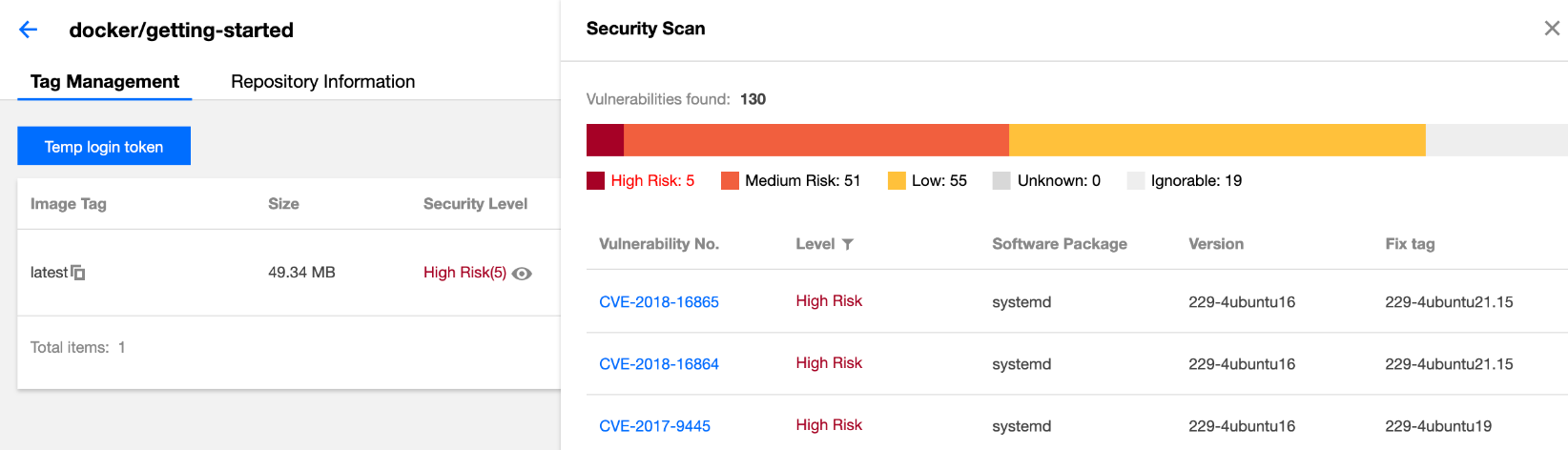
步骤3:查看扫描结果
安全扫描完成后,安全级别处将自动展示当前镜像内漏洞的最高等级及个数,可单击查看漏洞详情。如下图所示: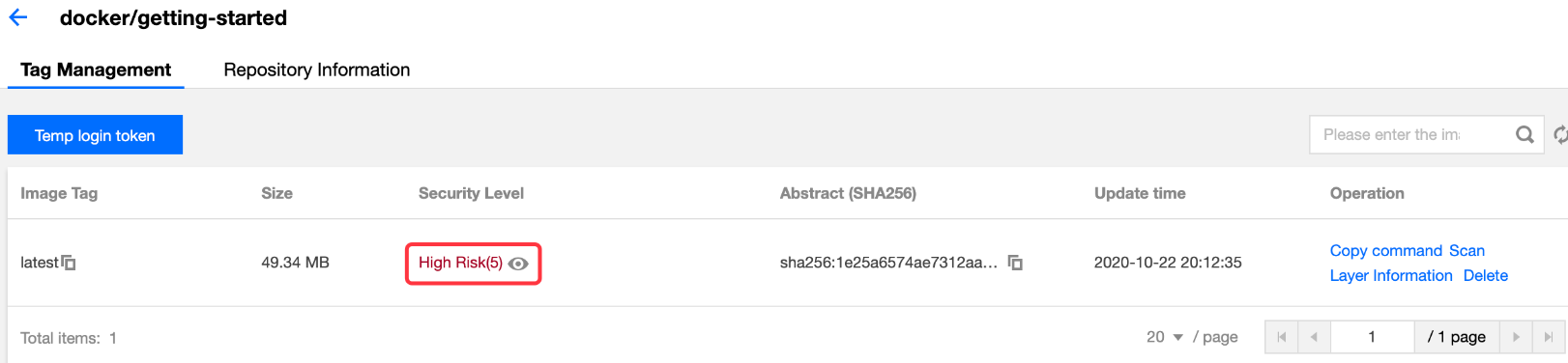
步骤4:重新触发扫描
文档反馈

